12 February 2021

Recently, I discovered via a Twitter thread that a single address can be the root email on two AWS accounts at the same time. How is this possible? Could my account be compromised as a result?
Let’s take a look at the thread in question:
It turns out the thread is technically correct, however there are a strict set of circumstances that allow for this to happen. This can only occur when you have:
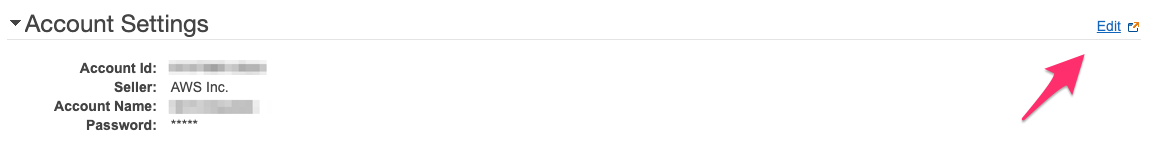
There’s actually an easy way to check which account type you have. If you log into your account as the root user, navigate to the “My Account” dashboard and click the “Edit” button on the “Account Settings” section.
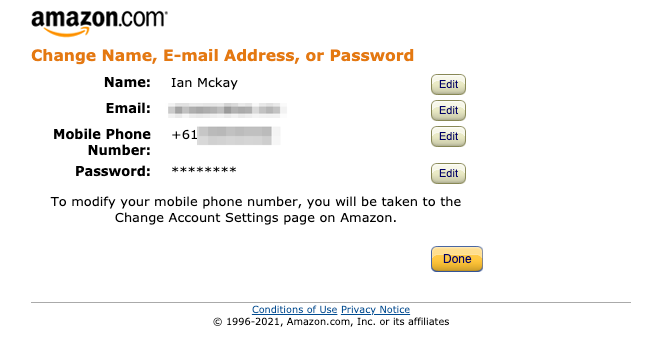
If the next page looks like this, you have an account that is linked to an Amazon.com account:
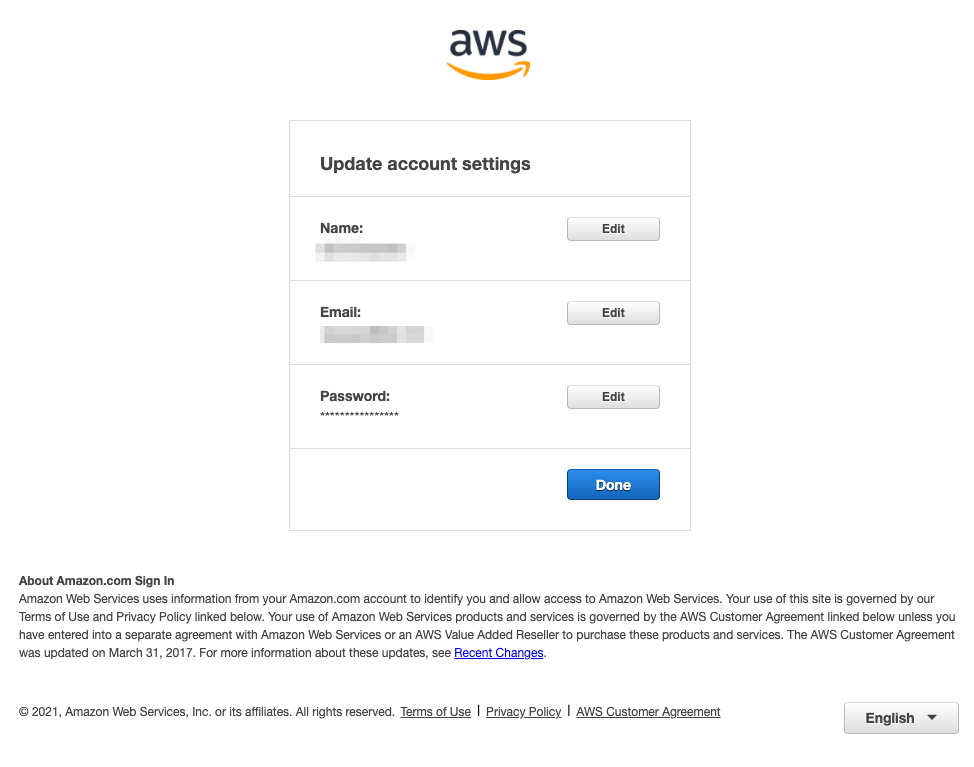
If the page instead looks like this, you have an account that is unlinked:
The only way to have the two AWS root accounts share the same email address is to change the Amazon.com linked account’s email address to that of the unlinked account. The reason this works is because Amazon.com authentication system is unaware of the unlinked AWS accounts and, for legacy reasons, the AWS authentication system will allow sign-ins via the Amazon.com accounts. This kind of problem doesn’t seem restricted to just AWS either.
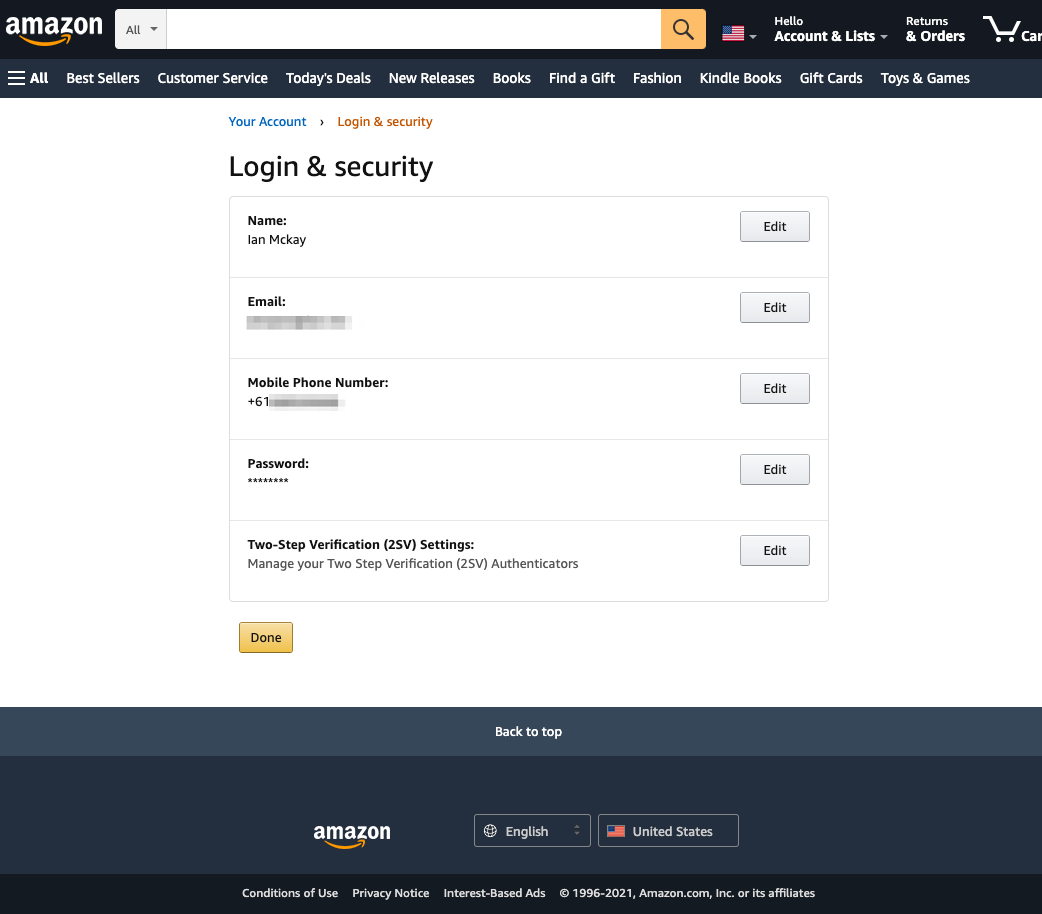
To do this, we first log onto the Amazon.com account and navigate to the account settings.
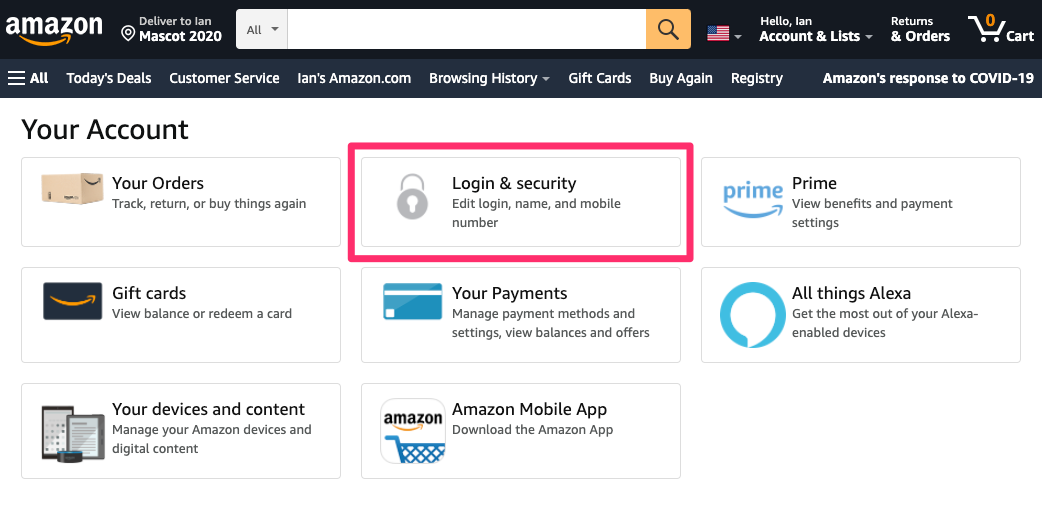
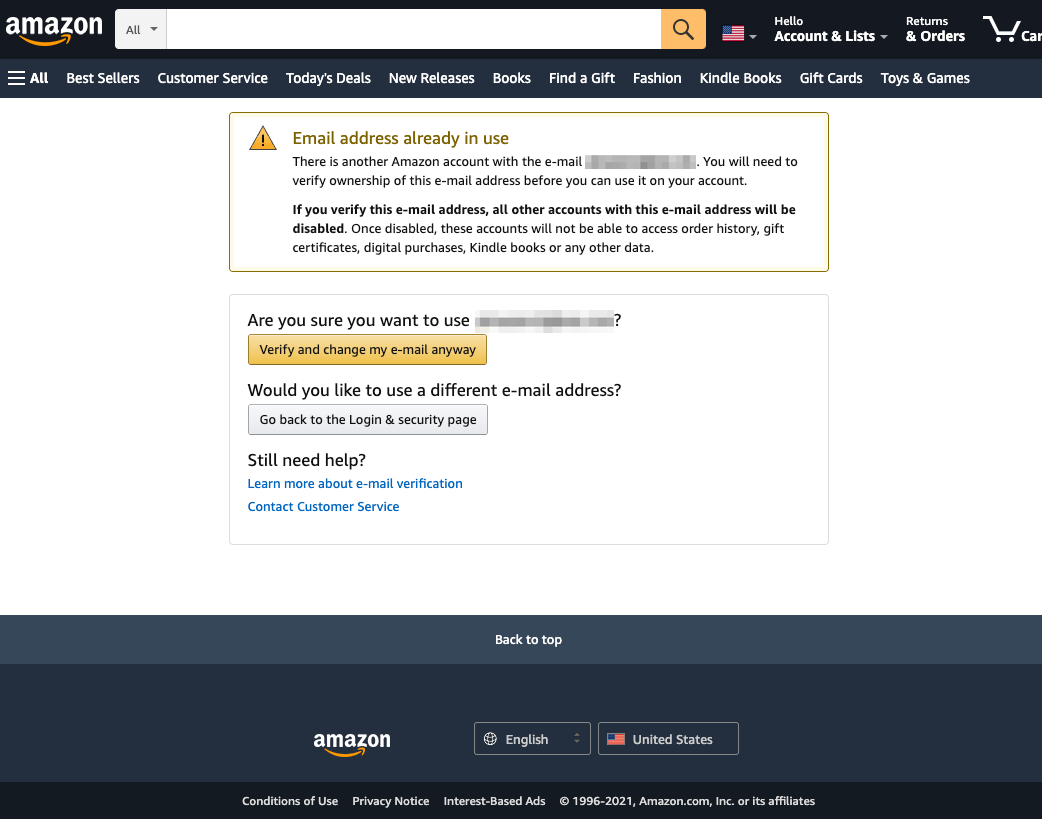
From here, go to “Login & security” then hit “Edit” on the email address field. You’ll then be prompted to set a new email address, so we enter the email address of the root user of the unlinked AWS account. This then needs to be verified via an emailed OTP code (notably not your TOTP tokens). Finally, re-enter your password to confirm the change. You have now set both AWS root accounts to the same email address.
This becomes slightly more interesting if you happen to have 2 Amazon.com linked accounts. If you attempt to change the email address of one to the other, you’ll actually see that there is a process to override / disable an existing Amazon.com account. As the Amazon.com login is used for root account access, in this case you would effectively lose access to one of your root accounts if you did this (so don’t!).
Effectively, you have now made the root account for the Amazon.com linked AWS account inaccessible. The account will still function as normal, IAM / SSO users can still log in and make changes, however if you attempt to use log in to the root account using its password it will fail. This is because when both accounts are sharing the same email address, the unlinked account is the one that will be authenticated against, regardless of whether the passwords are different or the same.
You can log in to the root account of the unlinked AWS account using its password, and perform all functions as normal. You can also use the reset password feature on the email address, which will reset the password on the unlinked AWS account, leaving the Amazon.com linked account untouched.
If you have had your fun and want to go back to a normal world, you can simply change the Amazon.com account email address back to its original form to restore access to the root account for its associated AWS account.
No, even though it certainly feels like it. You’ll note that all the email ownership security controls still apply during this process, so to perform this you will need control of the both email addresses involved, as well as any SMS / TOTP verification that is associated on the accounts.
If you feel you’d rather no longer be affected by the underpants problem, you may be able to raise a support ticket with AWS Support to migrate your account from a linked to an unlinked state. There are some implications of this, but presumably the AWS Support team will be able to explain those to you. Do take care when doing this as there are stories of people having problems with their Amazon.com accounts, such as being unable to reset or remove MFA, after this process occurs.
Under special circumstances, two AWS accounts could share the same root email address but it is not a security problem and will probably never happen to you.